Defcon 23
Defcon 23
 I attended BlackHat 2015 / DefCon 23 in Las Vegas. The badges were actual playable vinyl records with secret clues for the contest. They also made everyone look like Flavor Flav and were really awkward.
I attended BlackHat 2015 / DefCon 23 in Las Vegas. The badges were actual playable vinyl records with secret clues for the contest. They also made everyone look like Flavor Flav and were really awkward.
 My talk was discussing the details of my research with Xeno Kovah and Corey Kallenberg that resulted in Thunderstrike 2.
My talk was discussing the details of my research with Xeno Kovah and Corey Kallenberg that resulted in Thunderstrike 2.
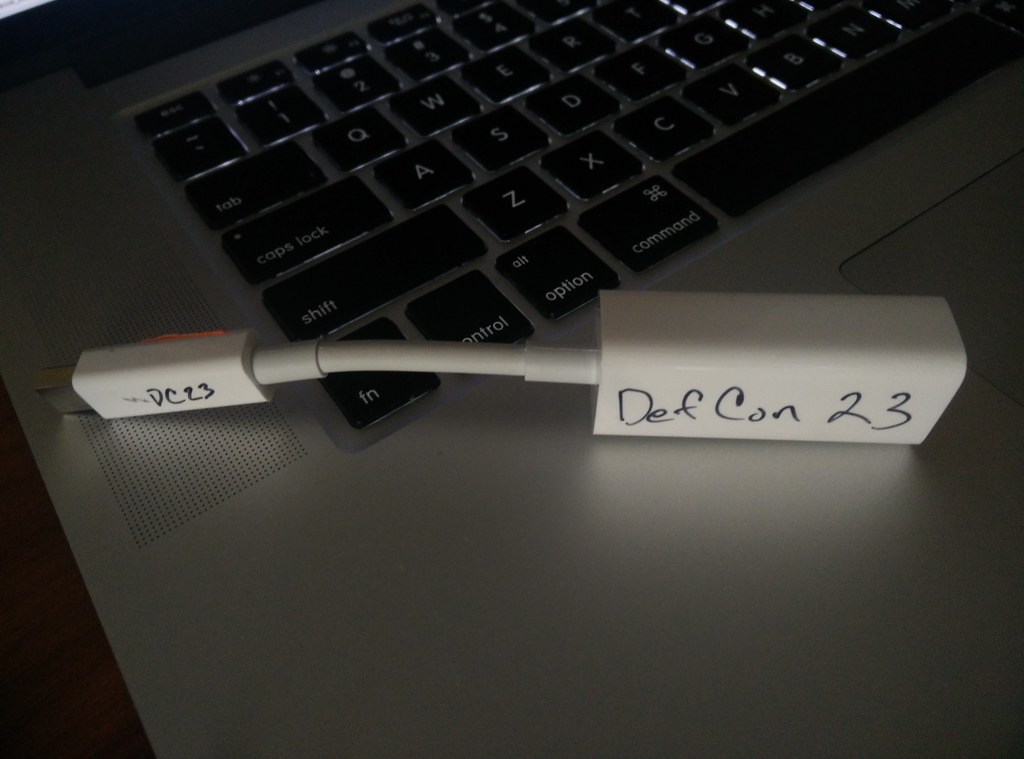 I offered to loan my Thunderbolt adapters to anyone who needed one. No one wanted to take me up on it after the Thunderstrike talk.
I offered to loan my Thunderbolt adapters to anyone who needed one. No one wanted to take me up on it after the Thunderstrike talk.
 Intel's Advanced Threat Research group cited our work on Thunderstrike 2 as a potential vector for firmware rootkits. They showed how such a rootkit could easily circumvent virtualization and hypervisor security.
Intel's Advanced Threat Research group cited our work on Thunderstrike 2 as a potential vector for firmware rootkits. They showed how such a rootkit could easily circumvent virtualization and hypervisor security.
 One of the highlights was seeing Soldier of Fortran and Big Endian Smalls discuss mainframe security.
One of the highlights was seeing Soldier of Fortran and Big Endian Smalls discuss mainframe security.
 The Rootpipe discussion was really depressing -- the vulnerability might go back to OSX 10.0. @osxreverser and Emil Kvarrhamar had shoutouts.
The Rootpipe discussion was really depressing -- the vulnerability might go back to OSX 10.0. @osxreverser and Emil Kvarrhamar had shoutouts.
 There was live transcription, which were often full of swear words and attempts to interact with the transcribers. Sometimes it worked.
There was live transcription, which were often full of swear words and attempts to interact with the transcribers. Sometimes it worked.
 Overall everyone was attempting to improve security. I'm not sure if this works.
Overall everyone was attempting to improve security. I'm not sure if this works.
A few more photos, although I wasn't taking very many on this trip.